- Does Windows 10 Education Have Remote Desktop
- Windows 10 Education Remote Desktop Free
- Windows 10 Education Remote Desktop Support
- Windows 10 Education Remote Desktop Login
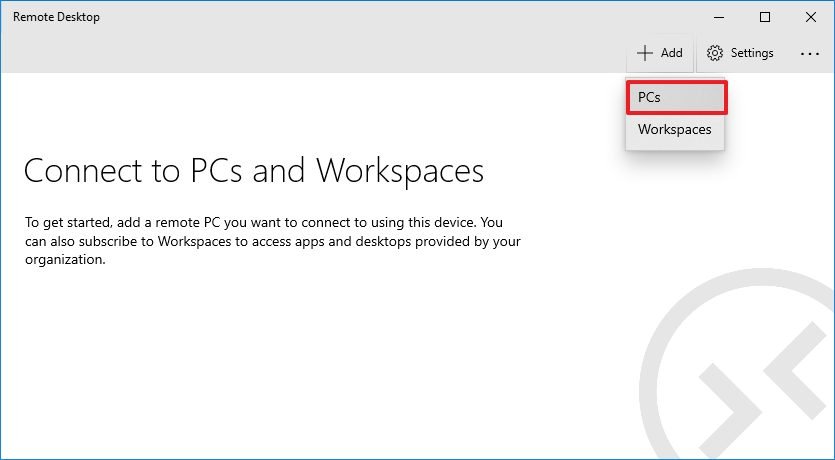
Microsoft Remote Desktop Free utility provided by Microsoft that enables remote desktop access to devices running Windows. Remmina Completely free for individuals and businesses – this is an open-source project and Linux users’ favorite. Remote Desktop Console & Agent. Remote desktop software has two components. The console and the agent. Next, find and run the file RDPWInst to check if you can run the remote desktop connection. In my test case, the above steps were enough to enable remote desktop to my Windows 10 home edition machine.
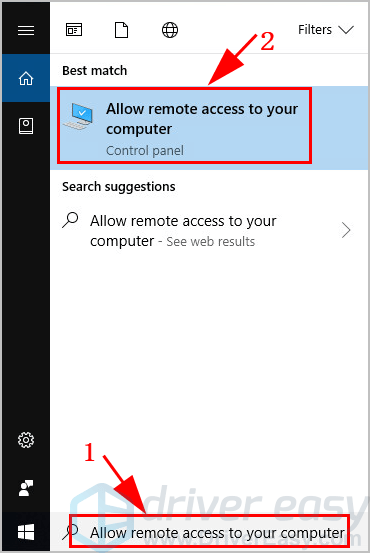
-->With Windows Autopilot, you can quickly transform a brand new device into a classroom-ready state—or reset existing devices to remove apps, settings and personal files—without physically having to touch the device. Windows 10 Pro in S-mode Windows 10 Pro in S mode has been designed with schools in mind. Click Select Users, located in the Remote Desktop section of the Remote tab. Click Add from the System Properties box. Type your myLSU ID and information for anyone else you would like to add. (This will allow Remote Desktop access to the computer which it is set.) 7. Click OK when finished. Return to Top Referenced from: Windows. On your local Windows 10 PC: In the search box on the taskbar, type Remote Desktop Connection, and then select Remote Desktop Connection. In Remote Desktop Connection, type the name of the PC you want to connect to (from Step 1), and then select Connect.
Applies to:
- Windows 10
Privacy is important to us, we want to provide you with ways to customize the OS diagnostic data, consumer experiences, Cortana, search, as well as some of the preinstalled apps, for usage with education editions of Windows 10 in education environments. These features work on all Windows 10 editions, but education editions of Windows 10 have the settings preconfigured. We recommend that all Windows 10 devices in an education setting be configured with SetEduPolicies enabled. See the following table for more information. To learn more about Microsoft's commitment to privacy, see Windows 10 and privacy.
We want all students to have the chance to use the apps they need for success in the classroom and all school personnel to have apps they need for their job. Students and school personnel who use assistive technology apps not available in the Microsoft Store for Education, and use devices running Windows 10 S, will be able to configure the device at no additional charge to Windows 10 Pro Education. To learn more about the steps to configure this, see Switch to Windows 10 Pro Education from Windows 10 Pro or Windows 10 S.
In Windows 10, version 1703 (Creators Update), it is straightforward to configure Windows to be education ready.
| Area | How to configure | What this does | Windows 10 Education | Windows 10 Pro Education | Windows 10 S |
|---|---|---|---|---|---|
| Diagnostic Data | AllowTelemetry | Sets Diagnostic Data to Basic | This is already set | This is already set | The policy must be set |
| Microsoft consumer experiences | SetEduPolicies | Disables suggested content from Windows such as app recommendations | This is already set | This is already set | The policy must be set |
| Cortana | AllowCortana | Disables Cortana * Cortana is enabled by default on all editions in Windows 10, version 1703 | If using Windows 10 Education, upgrading from Windows 10, version 1607 to Windows 10, version 1703 will enable Cortana. See the Recommended configuration section below for recommended Cortana settings. | If using Windows 10 Pro Education, upgrading from Windows 10, version 1607 to Windows 10, version 1703 will enable Cortana. See the Recommended configuration section below for recommended Cortana settings. | See the Recommended configuration section below for recommended Cortana settings. |
| Safe search | SetEduPolicies | Locks Bing safe search to Strict in Microsoft Edge | This is already set | This is already set | The policy must be set |
| Bing search advertising | Ad free search with Bing | Disables ads when searching the internet with Bing in Microsoft Edge. See [Ad-free search with Bing](#ad-free-search-with-bing | View configuration instructions as detailed in Ad-free search with Bing | View configuration instructions as detailed in Ad-free search with Bing | View configuration instructions as detailed in Ad-free search with Bing |
| Apps | SetEduPolicies | Preinstalled apps like Microsoft Edge, Movies & TV, Groove, and Skype become education ready * Any app can detect Windows is running in an education ready configuration through IsEducationEnvironment | This is already set | This is already set | The policy must be set |
Recommended configuration
It is easy to be education ready when using Microsoft products. We recommend the following configuration:
Use an Office 365 Education tenant.
With Office 365, you also have Azure Active Directory (Azure AD). To learn more about Office 365 Education features and pricing, see Office 365 Education plans and pricing. Aladdin xt plus 2 install guide.
Activate Intune for Education in your tenant.
You can sign up to learn more about Intune for Education.
On PCs running Windows 10, version 1703:
- Provision the PC using one of these methods:
- Provision PCs with the Set up School PCs app - This will automatically set both SetEduPolicies to True and AllowCortana to False.
- Provision PCs with a custom package created with Windows Configuration Designer - Make sure to set both SetEduPolicies to True and AllowCortana to False.
- Join the PC to Azure Active Directory.
- Use Set up School PCs or Windows Configuration Designer to bulk enroll to Azure AD.
- Manually Azure AD join the PC during the Windows device setup experience.
- Enroll the PCs in MDM.
- If you have activated Intune for Education in your Azure AD tenant, enrollment will happen automatically when the PC is joined to Azure AD. Intune for Education will automatically set SetEduPolicies to True and AllowCortana to False.
- Ensure that needed assistive technology apps can be used.
- If you have students or school personnel who rely on assistive technology apps that are not available in the Microsoft Store for Education, and who are using a Windows 10 S device, configure their device to Windows 10 Pro Education to allow the download and use of non-Microsoft Store assistive technology apps. See Switch to Windows 10 Pro Education from Windows 10 Pro or Windows 10 S for more info.
- Provision the PC using one of these methods:
Distribute the PCs to students.
Students sign in with their Azure AD/Office 365 identity, which enables single sign-on to Bing in Microsoft Edge, enabling an ad-free search experience with Bing in Microsoft Edge.
Ongoing management through Intune for Education.
You can set many policies through Intune for Education, including SetEduPolicies and AllowCortana, for ongoing management of the PCs.
Configuring Windows
You can configure Windows through provisioning or management tools including industry standard MDM.
- Provisioning - A one-time setup process.
- Management - A one-time and/or ongoing management of a PC by setting policies.
You can set all the education compliance areas through both provisioning and management tools. Additionally, these Microsoft education tools will ensure PCs that you set up are education ready:
AllowCortana
AllowCortana is a policy that enables or disables Cortana. Lookeen serial key. It is a policy node in the Policy configuration service provider, AllowCortana.
Note
See the Recommended configuration section for recommended Cortana settings.
Use one of these methods to set this policy.
MDM
- Intune for Education automatically sets this policy in the All devices group policy configuration.
- If you're using an MDM provider other than Intune for Education, check your MDM provider documentation on how to set this policy.
If your MDM provider doesn't explicitly support this policy, you can manually set this policy if your MDM provider allows specific OMA-URIs to be manually set.
For example, in Intune, create a new configuration policy and add an OMA-URI.
OMA-URI: ./Vendor/MSFT/Policy/Config/Experience/AllowCortana
Data type: Integer
Value: 0
Group Policy
Set Computer Configuration > Administrative Templates > Windows Components > Search > AllowCortana to Disabled.
Provisioning tools
- Set up School PCs always sets this policy in provisioning packages it creates.
- Windows Configuration Designer
Under Runtime settings, click the Policies settings group, set Experience > Cortana to No.
SetEduPolicies
SetEduPolicies is a policy that applies a set of configuration behaviors to Windows. It is a policy node in the SharedPC configuration service provider.
Use one of these methods to set this policy.
MDM
- Intune for Education automatically sets this policy in the All devices group policy configuration.
- If you're using an MDM provider other than Intune for Education, check your MDM provider documentation on how to set this policy.
If your MDM provider doesn't explicitly support this policy, you can manually set this policy if your MDM provider allows specific OMA-URIs to be manually set.
For example, in Intune, create a new configuration policy and add an OMA-URI.
OMA-URI: ./Vendor/MSFT/SharedPC/SetEduPolicies
Data type: Boolean
Value: true
Group Policy
SetEduPolicies is not natively supported in Group Policy. Instead, use the MDM Bridge WMI Provider to set the policy in MDM SharedPC.

For example:
Open PowerShell as an administrator and enter the following:
Provisioning tools
- Set up School PCs always sets this policy in provisioning packages it creates.
- Windows Configuration Designer
Under Runtime settings, click the SharedPC settings group, set PolicyCustomization > SetEduPolicies to True.
Ad-free search with Bing
Provide an ad-free experience that is a safer, more private search option for K–12 education institutions in the United States.
Configurations
Azure AD and Office 365 Education tenant
To suppress ads when searching with Bing on Microsoft Edge on any network, follow these steps:
- Ensure your Office 365 tenant is registered as an education tenant. For more information, see Verify your Office 365 domain to prove education status.
- Domain join the Windows 10 PCs to your Azure AD tenant (this is the same as your Office 365 tenant).
- Configure SetEduPolicies according to one of the methods described in the previous sections in this topic.
- Have students sign in with their Azure AD identity, which is the same as your Office 365 identity, to use the PC.
Note
If you are verifying your Office 365 domain to prove education status (step 1 above), you may need to wait up to 7 days for the ad-free experience to take effect. Microsoft recommends not to roll out the browser to your students until that time.
Office 365 sign-in to Bing
To suppress ads only when the student signs into Bing with their Office 365 account in Microsoft Edge, follow these steps:
Does Windows 10 Education Have Remote Desktop
- Configure SetEduPolicies according to one of the methods described in the previous sections in this topic.
- Have students sign into Bing with their Office 365 account.
Related topics
How secure is Windows Remote Desktop?
Remote Desktop sessions operate over an encrypted channel, preventing anyone from viewing your session by listening on the network. However, there is a vulnerability in the method used to encrypt sessions in earlier versions of RDP. This vulnerability can allow unauthorized access to your session using a man-in-the-middle attack.
Remote Desktop can be secured using SSL/TLS in Windows Vista, Windows 7, Windows 8, Windows 10 and Windows Server 2003/2008/2012/2016. *Some systems listed are no longer supported by Microsoft and therefore do not meet Campus security standards. If unsupported systems are still in use, a security exception is required.
While Remote Desktop is more secure than remote administration tools such as VNC that do not encrypt the entire session, any time Administrator access to a system is granted remotely there are risks. The following tips will help to secure Remote Desktop access to both desktops and servers that you support.
Basic Security Tips for Remote Desktop
1. Use strong passwords
Strong passwords on any accounts with access to Remote Desktop should be considered a required step before enabling Remote Desktop. Refer to the campus password complexity guidelines for tips.
2. Use Two-factor authentication
Departments should consider using a two-factor authentication approach. This topic is beyond the scope of this article, but RD Gateways can be configured to integrate with the Campus instance of DUO. Other unsupported by campus options available would be a simple mechanism for controlling authentication via two-factor certificate based smartcards. This approach utilizes the Remote Desktop host itself, in conjunction with YubiKey and RSA as examples.
Windows 10 Education Remote Desktop Free
3. Update your software
One advantage of using Remote Desktop rather than 3rd party remote admin tools is that components are updated automatically with the latest security fixes in the standard Microsoft patch cycle. Make sure you are running the latest versions of both the client and server software by enabling and auditing automatic Microsoft Updates. If you are using Remote Desktop clients on other platforms, make sure they are still supported and that you have the latest versions. Older versions may not support high encryption and may have other security flaws.
4. Restrict access using firewalls
Use firewalls (both software and hardware where available) to restrict access to remote desktop listening ports (default is TCP 3389). Using an RDP Gateway is highly recommended for restricting RDP access to desktops and servers (see discussion below). As an alternative to support off-campus connectivity, you can use the campus VPN software to get a campus IP address and add the campus VPN network address pool to your RDP firewall exception rule. Visit our page for more information on the campus VPN service.
5. Enable Network Level Authentication
Windows 10, Windows Server 2012 R2/2016/2019 also provide Network Level Authentication (NLA) by default. It is best to leave this in place, as NLA provides an extra level of authentication before a connection is established. You should only configure Remote Desktop servers to allow connections without NLA if you use Remote Desktop clients on other platforms that don't support it.
NLA should be enabled by default onWindows 10, Windows Server 2012 R2/2016/2019.
To check you may look at Group Policy setting Require user authentication for remote connections by using Network Level Authentication found at ComputerPoliciesWindows ComponentsRemote Desktop ServicesRemote Desktop Session HostSecurity. This Group Policy setting must be enabled on the server running the Remote Desktop Session Host role.
6. Limit users who can log in using Remote Desktop
By default, all Administrators can log in to Remote Desktop. If you have multiple Administrator accounts on your computer, you should limit remote access only to those accounts that need it. If Remote Desktop is not used for system administration, remove all administrative access via RDP, and only allow user accounts requiring RDP service. For Departments that manage many machines remotely remove the local Administrator account from RDP access at and add a technical group instead.
Click Start-->Programs-->Administrative Tools-->Local Security Policy
Under Local Policies-->User Rights Assignment, go to 'Allow logon through Terminal Services.' Or “Allow logon through Remote Desktop Services”
Remove the Administrators group and leave the Remote Desktop Users group.
Use the System control panel to add users to the Remote Desktop Users group.
A typical MS operating system will have the following setting by default as seen in the Local Security Policy:
The problem is that “Administrators” is here by default, and your “Local Admin” account is in administrators. Although a password convention to avoid identical local admin passwords on the local machine and tightly controlling access to these passwords or conventions is recommended, using a local admin account to work on a machine remotely does not properly log and identify the user using the system. It is best to override the local security policy with a Group Policy Setting.
To control access to the systems, even more, using “Restricted Groups” via Group Policy is also helpful.
If you use a “Restricted Group” setting to place your group, e.g., “CAMPUSLAW-TECHIES” into “Administrators” and “Remote Desktop Users,” your techies will still have administrative access remotely, but using the steps above, you have removed the problematic “local administrator account” having RDP access. Going forward, whenever new machines are added in the OU under the GPO, your settings will be correct.
7. Set an account lockout policy
Windows 10 Education Remote Desktop Support
By setting your computer to lock an account for a set number of incorrect guesses, you will help prevent hackers from using automated password guessing tools from gaining access to your system (this is known as a 'brute-force' attack). To set an account lockout policy:
- Go to Start-->Programs--> Administrative Tools--> Local Security Policy
- Under Account Policies--> Account Lockout Policies, set values for all three options. Three invalid attempts with 3-minute lockout durations are reasonable choices.
Best Practices for Additional Security
1. Do not allow direct RDP access to clients or servers from off campus.
Having RDP (port 3389) open to off campus networks is highly discouraged and is a known vector for many attacks. The options below list ways of improving security while still allowing RDP access to system.
Once an RDP gateway has been set up, hosts should be configured to only allow RDP connections from the Gateway host or campus subnets where needed.
2. Use RDP Gateways (Best Option)
Using an RDP Gateway is strongly recommended. It provides a way to tightly restrict access to Remote Desktop ports while supporting remote connections through a single 'Gateway' server. When using an RD Gateway server, all Remote Desktop services on your desktop and workstations should be restricted to only allow access only from the RD Gateway. The RD Gateway server listens for Remote Desktop requests over HTTPS (port 443) and connects the client to the Remote Desktop service on the target machine.
Utilize Campus RDP Gateway Service. This is the best option to allow RDP access to system categorized as UC P2 and lower. Includes DUO integration. RDP Gateway Service is provided by the Windows Team. Documentation is available here: https://berkeley.sharepoint.com/sites/calnetad/gateway.
The RDP Gateway Service also supports the new Remote Access Services requirement of the draft MSSND update (requirement 8), which requires the use of an approved service (i.e., RDP gateway, dedicated gateway, or bSecure VPN) for access to the UC Berkeley network from the public Internet.
Dedicated Gateway Service (Managed). Needed for rdp access to systems that are UC P4 or higher. Must also be configured for DUO
Some campus units use an IST managed VPS as an RD Gateway. A rough estimate might be that 30-100 concurrent users can use one RD Gateway. The HA at the virtual layer provides enough fault-tolerant and reliable access; however a slightly more sophisticated RD gateway implementation can be done with network load balancing.- Dedicated Gateway Service (Unmanaged). Installing and configuring RD Gateway on department run hardware.
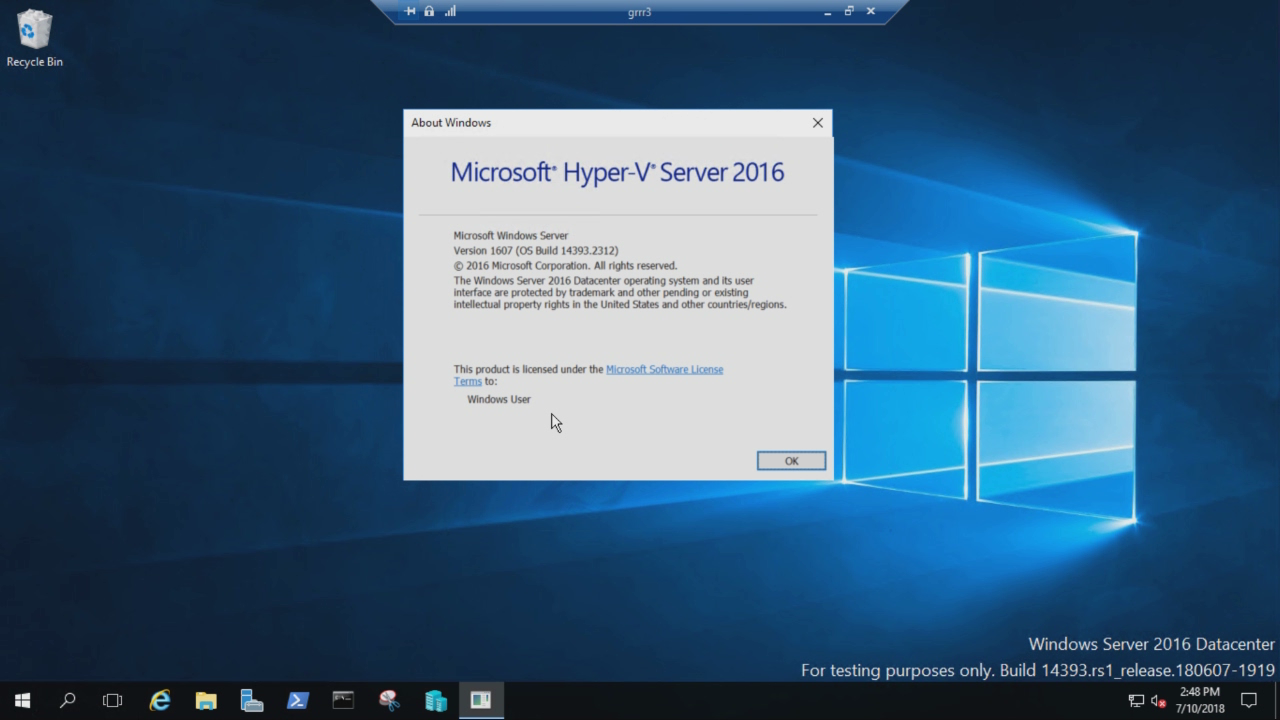
There are many online documents for configuring this embedded Windows 2016/2019 component. The official documentation is here: https://docs.microsoft.com/en-us/windows-server/remote/remote-desktop-se..
Installing the configuring, the role service is mostly as described; however, using a Calnet issued trusted Comodo certificate is recommended. Using a self-signed cert is ok for testing, and using a CalnetPKI cert can work if all clients have trusted the UCB root. The Comodo cert is usually better accepted so that your end users do not receive certificate warnings.
Configuring your client to use your RD Gateway is simple.The official documentation for the MS Client is here: http://technet.microsoft.com/en-us/library/cc770601.aspx
In essence, a simple change on the advanced tab of your RDP client is all that is necessary:
3. Change the listening port for Remote Desktop
Changing the listening port will help to 'hide' Remote Desktop from hackers who are scanning the network for computers listening on the default Remote Desktop port (TCP 3389). This offers effective protection against the latest RDP worms such, as Morto. To do this, edit the following registry key (WARNING: do not try this unless you are familiar with the Windows Registry and TCP/IP): HKEY_LOCAL_MACHINESYSTEMCurrentControlSetControlTerminal ServerWinStationsRDP-Tcp. Change the listening port from 3389 to something else and remember to update any firewall rules with the new port. Although this approach is helpful, it is security by obscurity, which is not the most reliable security approach. You should ensure that you are also using other methods to tighten down access as described in this article.
Windows 10 Education Remote Desktop Login
4. Tunnel Remote Desktop connections through IPSec or SSH
If using an RD Gateway is not feasible, you can add an extra layer of authentication and encryption by tunneling your Remote Desktop sessions through IPSec or SSH. IPSec is built-in to all Windows operating systems since Windows 2000, but use and management are greatly improved in Windows 10 (see: http://technet.microsoft.com/en-us/network/bb531150). If an SSH server is available, you can use SSH tunneling for Remote Desktop connections.
5. Use existing management tools for RDP logging and configuration
Using other components like VNC or PCAnywhere is not recommended because they may not log in a fashion that is auditable or protected. With RDP, logins are audited to the local security log, and often to the domain controller auditing system. When monitoring local security logs, look for anomalies in RDP sessions such as login attempts from the local Administrator account. RDP also has the benefit of a central management approach via GPO as described above. Whenever possible, use GPOs or other Windows configuration management tools to ensure a consistent and secure RDP configuration across all your servers and desktops.
By enforcing the use of an RDP gateway, you also get a third level of auditing that is easier to read than combing through the domain controller logins and is separate from the target machine so it is not subject to tampering. This type of log can make it much easier to monitor how and when RDP is being used across all the devices in your environment.
This work is licensed under a Creative Commons Attribution-NonCommercial 4.0 International License.
